Overview
Third-Party Risk Management (TPRM) is an advanced tool offered by Gartner, accessible through a subscription to Gartner.com, is a key tool for Chief Information Officers (CIOs) and their teams to manage risks associated with third-party vendors. This tool helps streamline due diligence, create controls to ensure third-party compliance, and establish ongoing risk management practices. Supported by Gartner’s research and expertise, TPRM aids legal, compliance, and risk management executives in developing effective strategies to mitigate third-party risks and maintain robust risk management.
Preparation

My Approach
Understanding Current Offering & Long Term Goal
Understanding high-level problem space based on insights from Insights Team of Gartner.
Also, analysing the gap between current offering and end-goal.
How Each Persona Works in Orchestration.
Understanding different types of personas with their roles and responsibility.
Types of Processes & Risk Involved.
Findings related to all the types of risks, impact of risks and processes involved in assessing the Third-party Risk.
Conceptualisation, Defining Success Metrics & User Flows.
Based on information in hand & through understanding of the problem statement, defined success metrics and designed possible user flows.
Design & Controlled Testing
We landed to the concept named “Workflow” and then started with designs, followed by user-testing in controlled group via prototype.
What problem are we addressing?
This project aims to provide organizations with a comprehensive solution to assess, monitor, and mitigate security risks posed by third-party vendors. The goal is to ensure that all external partnerships, particularly with vendors, do not expose the organization to security vulnerabilities.
Who are we solving this for?
Our primary audience consists of CIOs, CISOs and their team members, who are responsible for ensuring that the organization remains secure when engaging with external vendors. These professionals must constantly monitor, assess, and address risks to uphold the integrity and security of their organization’s infrastructure.
Why are we building this?
In today’s interconnected environment, onboarding new vendors or managing existing ones poses a significant risk to the security posture of an organization. By creating this tool, we empower teams to gain visibility into vendor-related risks and take proactive measures to mitigate them.
How will we achieve this?
By providing platform that provides a structured and comprehensive assessment of third-party vendors. The tool will enable organizations to evaluate security risks in a standardized manner, allowing them to take appropriate actions & informed decisions—whether that involves implementing additional controls internally or collaborating with vendors to enhance their security measures.
About The Project
The long-term goal of this project is to establish a robust platform that becomes the go-to solution for organizations to fully manage and mitigate security risks associated with third-party vendors. This platform will provide continuous, real-time risk assessment, automated mitigation strategies, and seamless integration with an organization’s broader security and compliance infrastructure. It will evolve into an indispensable tool for CIOs and their teams to ensure vendor security, regulatory compliance, and proactive threat prevention, ultimately reducing the overall attack surface of the organization.
Understanding Current Offering and Long Term Goal
Understanding Gaps between current offering and goal

Workflow for CIOs and Team
UX Case Study
Tool for Third Party Risk Management (TPRM)
LIVE
My Role and Duration
UX Designer | Gartner
Research, Interaction, Visual Design, Prototype and Testing
April 2024 to September 2024
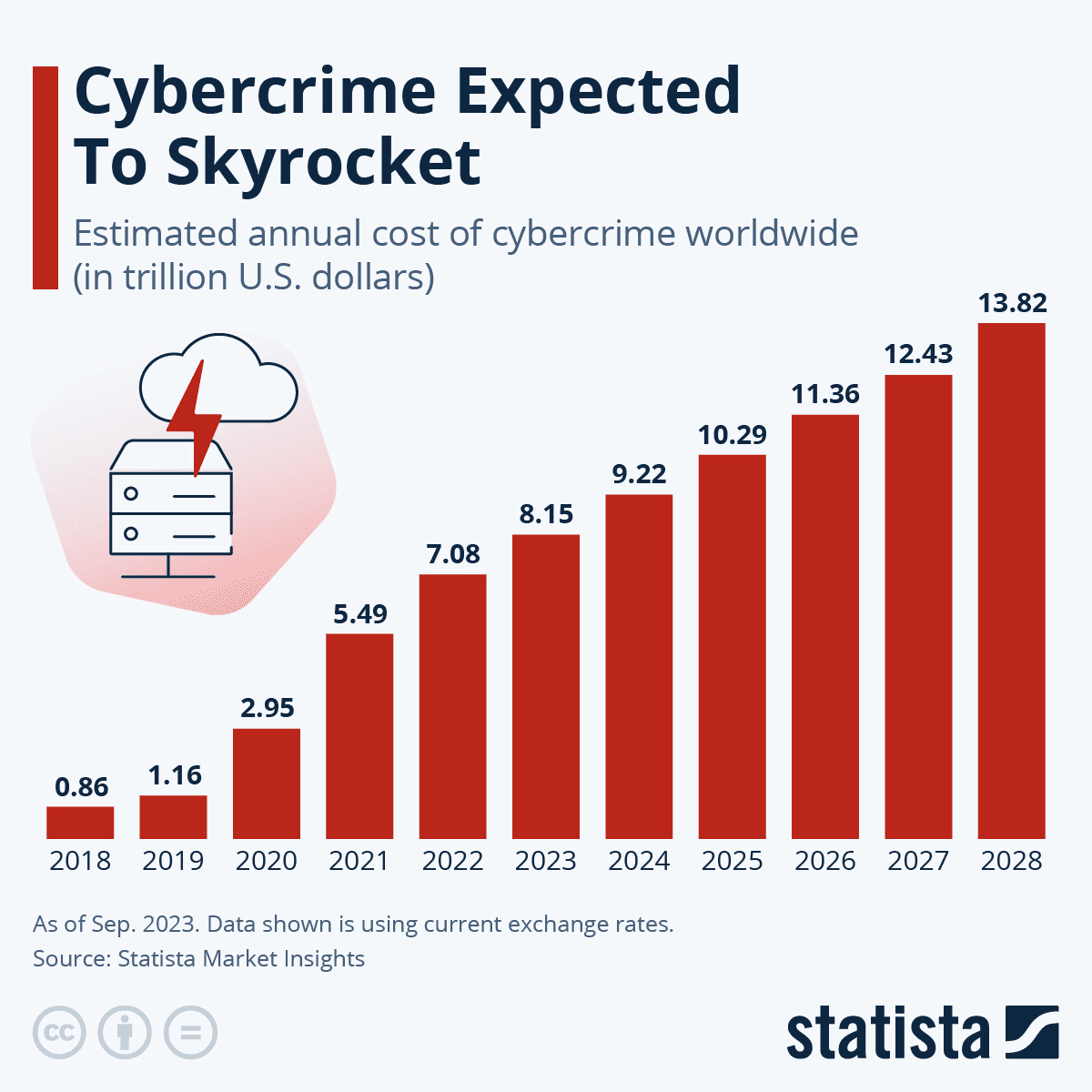
"Security Risk Management is a major focus for Gartner's security clients, especially in light of recent data and incident reports highlighting a rise in cyber security breaches."


Currently, the platform lacks a standardized framework for assessing third-party vendors. Assessments are inconsistent and vary across teams, leading to gaps in identifying and managing potential security risks comprehensively
No Structured Approach to Assessment
The current solution does not provide organizations with a clear methodology to evaluate or verify the security controls of vendors. Without the ability to audit vendor security practices effectively, organizations are left uncertain about the actual risk exposure.
No Way for Organizations to Assess Vendor Controls
The platform does not offer a centralized dashboard or reporting system that aggregates risk metrics from all vendors. This fragmentation makes it difficult for organizations to compare risks, track performance, and prioritize remediation efforts across multiple vendors
No Consolidated View of Risk Metrics or Scores Across Vendors
There is no built-in mechanism for delegating tasks or corrective actions to relevant stakeholders within the organization or the vendor. This limits the efficiency of the risk management process, as critical steps may be delayed or neglected without clear assignment of responsibilities
Inability to Delegate Actions to Other Stakeholders





Personas and Their Role in System
CIOs
Typically use the platform’s data sets and reports to make informed & strategic decisions.
CISOs and Head of Cybersecurity Risks & Compliance
Oversee their teams to ensure accurate performance tracking and close monitoring of metrics, particularly emerging risks with any vendor in operation with their organization. They focus on developing solutions to manage these risks effectively, ensuring a smooth and secure relationship with third-party vendors.
Team members, such as Cybersecurity Specialists, Analysts, and System Administrators, etc.
Play a crucial role in evaluating vendors. They are responsible for identifying, managing, and monitoring risks associated with third-party relationships throughout the assessment process.

Cameron Williamson
CISO
3rd party risk feels like a blackbox, I have to trust a lot of people, which is not inherent to my position.
Age:
45 -55
Device:
Laptop, Tablet, Mobile
Reports To:
CIO
Proactive
Full of Energy
Detail Oriented
Focused
Key Responsibilities
Data privacy, product security, data loss prevention (DLP), identity and access management (IAM).
Keeping the assessment process as lean as possible while effectively managing risk Responsibilities.
Establishing policy and maintaining governance with third-party vendors.
Reviewing Cyber Security team reports.
Report out on risk to the board in the future as he scales his team.
Basic Expectations (Table Stakes)
Streamlined Experience -
One view dashboard to look for Third Party Risk
Trustworthy 'surface level' data
Quick reporting on any breach or increased risk
Vendor Data -
3rd party audits or certification
Service Organization Control 2 (SOC-2) Type-2 Report
Ability to relate assessment questionnaire data to his industry
Risk classification
Mitigation & Resolution -
Identification of additional controls required & rationale
Cyber Security risk advice on acquisitions
Reporting -
Risk exposure analysis suitable for Board consumption
Relevant alerting and escalation paths by business line
Pain points
Untrustworthy Data: Inaccurate or outdated information undermines our ability to make informed decisions and manage risks effectively.
Lack of Instant Insights: The absence of readily accessible, actionable insights hampers our ability to quickly understand and respond to emerging security threats.
Inability to Delegate for Further Action: The current system does not facilitate the seamless delegation of tasks and follow-up actions.
Irrelevance to Industry-Specific Needs: The tools available are not adequately tailored to our specific industry requirements. This misalignment results in a lack of pertinent information and guidance.
Lack of Integrated Organizational Platform: The absence of an integrated solution for communication and joint efforts leads to inefficiencies and fragmented workflows.
Centralized Vendor Risk Assessments: Hosting all vendor risk at a single, accessible location would improve our ability to monitor and review vendor risks comprehensively.
Small Vendors Inclusion: new vendors in market are hard to find on platforms that makes it difficult to assess and often receive high-risk evaluations by default, is crucial.

Cara June
Head of Cybersecurity Risk & Compliance
No time to rest, it feels like I am constantly on treadmill and the time I stop everything will fall apart.
Age:
37 -47
Device:
Laptop, Tablet, Mobile
Reports To:
CISO
Proactive
Agile
Decision Maker
On Toe’s
Key Responsibilities
Building relationships and communicating with a network of stakeholders, vendors, and other team members.
Delegating - staying high-level, out of the weeds and monitoring teams work.
Skilfully juggling with legal needs, CISO needs, clients, and regulatory requirements.
Balancing between Third Party Risk, Security Risk and Compliance.
Monthly risk monitoring of vendors.
Reporting out on risks at a moment's notice.
Assigning team to work with problem vendors.
Basic Expectations (Table Stakes)
Trusted Information -
Vendor information must be comprehensive
Must be sure she's communicating accurate information to her team
Vendor Coverage -
Flexibility to customize to her unique Third Party
Risk Program
Actionable Insights -
Identify high risk vendors and opportunities to
reduce risk
Alert stakeholders when there's something to be aware of
Understand/communicate/escalate and navigate via a risk they are from a particular vendor
Report She Share Should Be -
Easy to run, simple to share and Meaningful
One view of overall risk
Pain points
Lack of Vendor Coverage: Inability to trust the information (misleading ratings, etc.)
Non-structured Assessment Types: Completely unfamiliar assessment compared to her process.
Non Sharable Format of Reports: Can't report or share out
Shallow features: Just one more dashboard with non-actionable data.
No Alerts and Actionable Insights: Don’t get timely alerts or notification so that she can engage earlier with at-risk vendors and make decisions at all business levels
Non User-friendly Tool: Complicated, distributed platform that increase task to look for different types of data at different places.
No Team Collaboration: No platform that allow organisation to function as one team on same tool.
Here’s a breakdown of various team members, along with their designations and responsibilities. Each of these roles contributes to the efficient operation and strategic management of an organisations IT environment, working together to support the CIO’s and leadership objectives.
Cybersecurity Specialist:
Protect the organization from cyber threats by implementing security measures, monitoring systems for vulnerabilities, and responding to security incidents.
Software Developer:
Design, develop, and maintain software applications tailored to business needs. Write and test code, debug issues, and collaborate with other developers and stakeholders.
Systems Administrator:
Install, configure, and support hardware and software systems. Manage server environments, ensure system reliability, and perform regular maintenance and updates.
Data Analyst/Scientist:
Analyze and interpret complex data sets to support business decisions. Develop data models, create reports, and provide actionable insights based on data trends.
IT Support Specialist:
Provide technical support to end-users, troubleshoot hardware and software issues, and resolve IT-related problems. Assist with installation and maintenance of technology systems.
IT Manager:
Oversee specific IT functions or departments (e.g., infrastructure, applications). Manage day-to-day operations, ensure system performance, and align technology with business needs.
IT Analyst:
Analyze and assess IT systems and processes. Provide insights and recommendations for improvements, and support decision-making through data analysis and reporting.
Network Administrator:
Manage and maintain the organization’s network infrastructure and firewalls. Ensure network security, performance, and connectivity.
Data Analyst/Scientist:
Analyze and interpret complex data sets to support business decisions. Develop data models, create reports, and provide actionable insights based on data trends.
Business Analyst:
Act as a liaison between IT and business units. Gather and document business requirements, analyze processes, and ensure technology solutions align with organizational goals.
The research journey began with a comprehensive team Knowledge Transfer session to ensure alignment on project goals and user needs.
This was followed by observing and analyzing initial user interviews stored on Dovetail, the internal platform used to archive all user interviews. The analysis provided valuable insights into user behavior and pain points.
To gain a deeper understanding, focus group interviews were planned and conducted with security experts, to explore the specific terminology, functions, and challenges security professionals face. This helped in uncovering opportunities to enhance functionality and tailor solutions to their workflow.
The Research
Worked closely and in sync with the entire product team to form the logics and workflows for vendor assessments. This collaboration ensured that the flows were not only user-centric but also aligned with the overall product goals, creating a seamless and efficient process for evaluating and managing vendor risks. With regular alignment with TPRM Leadership.
Research Insights & Actions
There are 4 different types of steps involved in assessment of each vendor, which is performed by difference personas in the team of CIOs and CISOs.
We learned about the systematic approach taken by security professional to assess a vendor, their interdependencies and impact.
The assessment process is primarily structured around three core risk metrics: Inherent Risk, Vendor Controls, and Residual Risk.
These metrics encompass a wide range of sub-metrics, and their combinations generate various insights for identifying and assessing high-risk vendors.
Each metric is broken down into distinct categories such as Operational, Business Continuity,Information Security/Cyber, Legal/Regulatory/Compliance, Technology, Reputational and Strategic Risks. Within these categories are multiple risk types, each with specific descriptions and characteristics.
The intricate combinations of these risk types allow us to map diverse risk scenarios to specific categories. This mapping enabled the development of precise formulas used to evaluate and assign scores to each identified risk type. These formulas ultimately contribute to calculating the final values of each major risk metric, providing a comprehensive risk profile for each vendor.





Conceptualisation | Success Metrics Defined | User Flows.
Brainstorming and Finalising Base Concept with Team
I started creating the information architecture and user-flows of concepts for primary use cases. After having a go-ahead from the Product Manager, Developers, and other Stakeholders on the proposed solution, logic and user journey, we proceeded to break down the journey into manageable tasks and started with iterations.
Linear or Non-Linear User Flows?
Initially we had two different approaches to either go with and linear stepper workflow which user (multiple members of CIO team) will go through one-after-one and won’t be allowed to flexibly assess vendors any metrics at any moment.
or
Another option, to give flexibility to user (multiple members of CIO team) to assess any metric they need at any point in time via non-linear workflow.
“
Finally we went ahead with Hybrid Workflow i.e. mix of both linear and non-linear user-flows.





Iterations
This project was executed in phases, involving multiple levels and numerous iterations throughout the designing process.


The Journey Begins With
“Insightful Vendor Profile”
Initially, the Vendor Profile consisted of only "About" and "News" widgets.
Expanded the profile beyond static information to provide dynamic insights that enhance user engagement and utility.
Added insightful data widgets to empower users/organizations to make informed decisions about each vendor and their reliability.
Introduced real-time data feeds and analysis tools that deliver actionable insights on vendor performance, compliance, and risk factors, ensuring decision-makers can evaluate vendors with confidence.
Centralized all key metrics relevant to third-party vendors, catering specifically to security professionals for easier access and context relevance.
Consolidated critical security and risk metrics into one section, reducing cognitive load and enhancing workflow efficiency for professionals dealing with compliance and risk assessments.
Employed visual elements such as charts, graphs, icons, and color schemes to facilitate rapid data comprehension, comparison, and decision-making.
Focused on intuitive data visualization techniques, ensuring information is not only accessible but also digestible at a glance, allowing users to quickly scan through vendor metrics, compare performance, and identify trends.

The Home to Workflow Journey
“Your Assessment”
Consolidated all steps of the third-party vendor assessment process into a unified stepper format.
This progress indicator not only tracks assessment completion but also serves as a guide, proactively informing users of upcoming steps and helping them manage their workflow effectively.
By ensuring locked steps are visually distinct and accompanied by actionable guidance, the user experience is enhanced, preventing bottlenecks and ensuring the assessment is completed without unnecessary delays.
Downloadable Risk Summary Report allows for efficient internal communication by enabling users to export and present vendor risk insights outside of the TPRM platform, catering to decision-makers who prefer offline reports or meetings.
Introduce an autoscroll feature that automatically brings users to the current step they are working on, keeping them focused and directly engaged with the task at hand.
Initial Step of the Workflow
“Inherent Risk(IR) Assessment”
The Inherent Risk (IR) assessment consists of 9 carefully curated questions developed by the Gartner TPRM specialist team, designed to evaluate the organization's risk exposure with a particular vendor.
The page layout is divided into two sections: the left side serves as the working area for responding to questions, while the right side displays real-time impact of responses and a summary of the Inherent Risk.
Auto-save functionality ensures a seamless user experience by preventing data loss, reducing frustration, and enabling users to resume where they left off without disruption.
Given that organizations have offline connections with vendors, an edit option is provided to allow users to manually adjust the system-generated Inherent Risk score if they believe it should be changed for Accuracy.

Workflow & Design Decisions
The Solution

Step share by both user and vendor
“Vendor Control Assessment”
On this step user identify the risks by flagging the responses of vendor control questionnaire, which are 89 set of questions carefully curated questions developed by the Gartner TPRM specialist team, both user and vendor work in sync to complete this step.
Offering flexibility by multiple options. If the vendor is already on the platform, the user can request an attested questionnaire for quicker task completion, otherwise self-import or manually enter the responses.
The workflow anticipates various scenarios, applying a well-structured "If this, then that" logic to handle different outcomes. A "Self Import" feature is introduced, enabling users to complete tasks independently and progress through the workflow without waiting for vendor responses.
Proactive disclosure of CTAs ensures users are guided effectively throughout the process. Noise is minimized on each step, focusing on the primary task at hand while disregarding non-essential elements.
Given that the questionnaire can be lengthy and require significant time and attention, an auto-save feature is implemented throughout the journey to preserve progress.



2 alike steps performed by different personas
“Evaluate Treat Identified Risk(s) & Treat Identified Risk(s)”


The steps "Evaluate" and "Treat Identified Risks" are handled by different user personas, so these steps were intentionally kept separate to reflect their distinct workflows.
In the MVP, functionality was added to allow users to comment after every major decision-making step in the workflow. This feature encourages seamless team collaboration. Future plans include developing a comprehensive Team Collaboration model as a separate project.
These customized tables not only improve usability but also serve as a decision-making hub, providing users with all necessary data points in a concise format. The goal is to ensure that decisions are both efficient and accurate, considering their impact on the vendor's risk profile.

Impact Areas
Post Workflow

The key impact areas include the Dashboard, Manage Portfolio Tab, and Vendor Profile screens, where widgets dynamically adapt to reflect updated information following the successful assessment of each vendor.
These are designed to be highly responsive, automatically refreshing to display the most recent assessment results. This ensures that users always have access to up-to-date data on vendor risk metrics, and overall portfolio health, enhancing decision-making and strategic oversight.
The Workflow Project is designed with a user-centric approach, focusing on streamlined decision-making, flexibility, and collaboration. Key UX decisions were made to enhance the experience across various critical screens and processes.
These UX decisions aim to create an intuitive, efficient, and collaborative experience, ensuring users can assess and manage vendor risks with ease and accuracy.
Throughout the project, the product was tested at various stages to ensure continuous feedback and refinement.
Prototypes were shared with key stakeholders on a weekly basis to gather feedback on the product’s functionality, content, and interactivity. This iterative testing process allowed for quick adjustments based on stakeholder insights, ensuring that the product aligned with user needs and expectations at each stage of development.
Unmoderated user testing was conducted with security experts consulting on the project. These experts interacted with the tool to complete hypothetical tasks, such as assessing dummy vendors, providing valuable insights into real-world usability. This phase helped identify pain points and refine the user experience based on practical, industry-specific feedback.
Before the product’s release, Beta testing was carried out with a group of 10 randomly selected industry experts from Gartner’s database. In this phase, participants used the Workflow tool to add and assess the third-party vendors their organizations operate with. This real-world testing ensured that the product was robust, functional, and tailored to meet the needs of professionals managing third-party vendor relationships in their organizations.




Usability Testing
Success Metrics Achieved
“These metrics are based on the data analysed after the controled release with total 40 users of TPRM”
1. Simplicity is Strength
As a designer, we are often lured by attractive, trendy and out of the box designs. But, We must always remember the ‘why’. The primary goal is to understand the user, their problems and then come up with a design that solves it.
2. Prioritize
Create a strategic plan to launch an MVP. This helps deal with out-of-scope requests that could potentially derail the project and helps deliver a quality product in time.
3. Seek Out Feedback Early and Continually
The trouble with most of us is that we would rather be ruined by praise than saved by criticism. Keeping the stakeholders/users in loop and testing solutions in whatever form (paper, low-fi or hi-fi) as early as possible saves ample amount of time and re-work.
Project Learnings
82%
28/34 Completed Assessmnet
< 7 Days
Time Taken to Complete Assessment
85%
34/40 Users Adopted Platform

Let’s Connect
Feel free to reach out for collaborations or just a friendly hello

or
